Hello again! There has been a lot of discussion and curiosity about the recent news that iOS 16 will have an enhanced Hidden assets feature. According to the press releases, this feature will allow a user to lock hidden assets behind the device Passcode, Touch ID, and/or Face ID. The question I believe most of us forensicators are asking ourselves, what does that mean for us, and can we get access to the files after a device acquisition?
The test device used:
- iPhone 12 [iPhone13,3] (A2341)
- iOS 16.0 (20A5303i) beta 6/22/2022
**Update 10/3/2022**
- iPhone 12 [iPhone13,3] (A2341)
- iOS 16.0.2 (20A380)
The following tools were used to create data acquisitions and were used to analyze the acquired data:
- iTunes 12.12.4.1
- 3uTools Version 2.60 & 2.63
- Artifact Examiner (ArtEx) 2.3.0.0 & 2.4.12.0
Unencrypted iTunes backup acquisitions were the only type of acquisitions used for this research and testing.
On Monday, July 4th, 2022, I upgraded the iPhone X [iPhone10,3] (A1865) to an iPhone 12 [iPhone13,3] (A2341). During that time, I also changed the Apple ID that was being used from Ben Scooter Gates to John Scooter Wick. After updating the device, I used it for some artifact generation, which included capturing and editing assets, and traveling around town.
On Tuesday, July 26, 2022, at approximately 8:19 PM, I performed an iCloud backup, signed out of Find My, and signed out from using the current Apple ID. At 8:20 PM, the device settings were accessed, and the device was factory reset. At 8:24 PM, the device finished the reset, and the device was restored as a new device and exited the setup at 8:32 PM. The previous Apple ID (John Scooter Wick) was used to log into the test device and iCloud Photos were synced.
Device Settings and Properties List (plist)
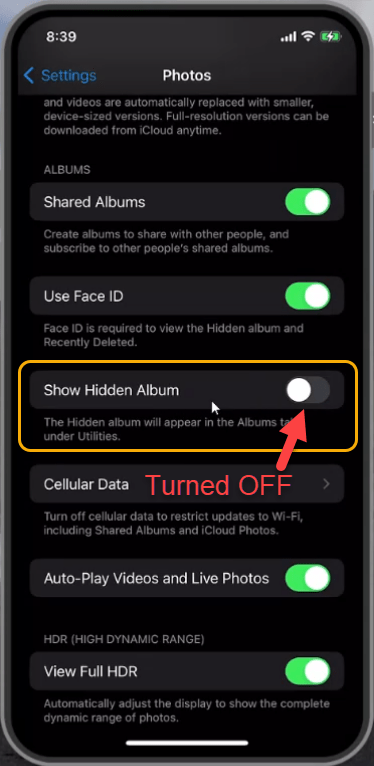
If we navigate to settings > Photos, we can access some of the settings for the Photos Application (com.apple.mobileslideshow). We can see in Figure #2 the new toggle switch in iOS 16 titled, Use Face ID. The description for this toggle switch indicates when turned on, “Face ID is required to view the Hidden album and the Recently Deleted.” In Figure #2 the toggle switch is in the ON position.

If the device is not using Touch ID or Face ID, then this setting will be titled Use Passcode. If the device is not using a Passcode, Touch ID, or Face ID, then this setting will be OFF by default and grayed out. I searched but was not able to find the Use Face ID setting toggle switch in a plist.
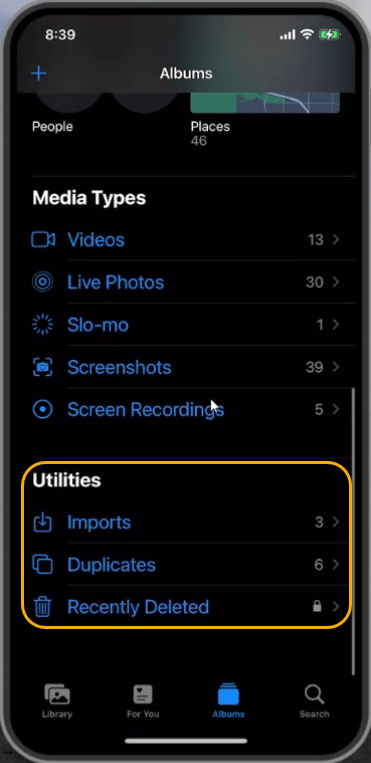
Show Hidden Album
I want to remind everyone about the other toggle switch we can see in Figure #2 titled, Show Hidden Album. The description for this toggle switch indicates when turned on, “The Hidden album will appear in the Albums tab, under Utilities.” In Figure #3.1 the toggle switch is in the ON position. In Figure #3.2 we can see the Albums tab and under the Utilities section we can see the Hidden utility.


In Figure #4.1 the toggle switch is in the OFF position. In Figure #4.2 we can see the Albums tab and under the Utilities section we cannot see the Hidden utility anymore.
How can we determine the Show Hidden Album device settings after a device acquisition has occurred?
To do that, we will analyze the following properties list (plist) being stored at the following location:
- \private\var\mobile\Library\Preferences\
- com.apple.mobileslideshow.plist
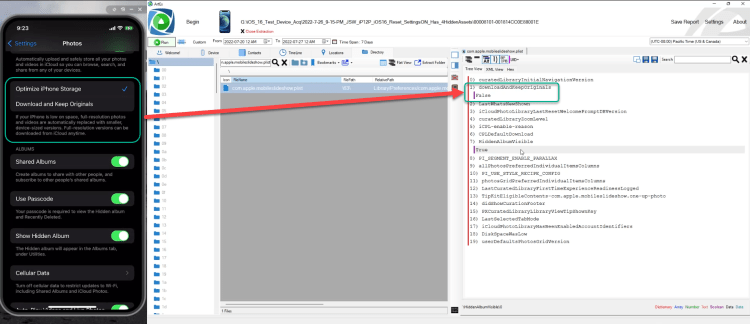
In Figure #5 we can see the device settings and the plist being displayed within ArtEx. We can see the HiddenAlbumVisible key is indicating True, meaning the toggle switch is turned ON.
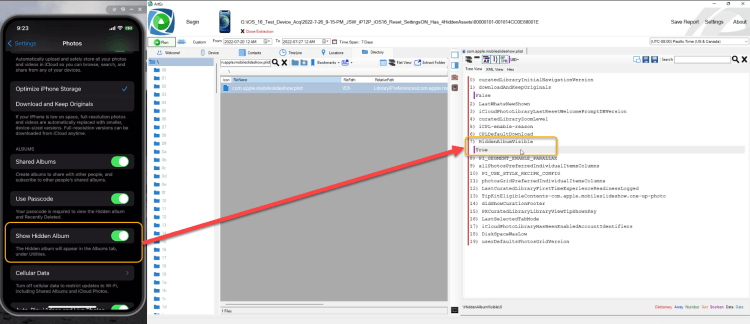
In Figure #6 we can see the device settings and the plist being displayed within ArtEx. We can see the HiddenAlbumVisible key is indicating False, meaning the toggle switch is turned OFF.

BONUS: Additionally, being stored within this plist, we can see the device setting for Download and Keep Originals and the downloadAndKeepOriginals key. We can see the downloadAndKeepOriginals key is indicating False, meaning the device setting is not selected, indicating Optimize iPhone Storage is the selected setting.
These results are consistent with what has been observed in my testing of iOS 14, 15, and 16.
Accessing the Passcode, Face ID, or Touch ID protected Hidden assets
First, let me point out, when assets are selected to be Hidden, a new album is NOT created. In my opinion, the most critical change to be aware of is when an asset is marked as Hidden, the value within Photos.sqlite > ZASSET table > ZHIDDEN column is changed from zero (0) to one (1) marking the asset Hidden. This is the same behavior that has been observed during research within iOS 14 and iOS 15 Photos.sqlite.
In Figure #8, we can see a sample from Photos.sqlite were some assets have a ZHIDDEN value of 1, which again indicates these assets are Hidden. A few of the assets have a ZHIDDEN value of 0 indicating these assets are not hidden. We can also see a case statement which is included in the Photos.sqlite query that allows us to interpret/decode those values.

In Figure #9, we can see the steps taken on the test device to access the Hidden assets. This is an example of a device that has Face ID turned off and the device is protected only by a passcode.

Figure #10 is a video demonstrating the settings and what might happen if Hidden assets are accessed when Face ID is not recognized. The current version of iOS 16 allows the user to bypass the Face ID requirement and enter the device passcode to gain access to the Hidden assets.
Forensically accessing Hidden assets
First, I would like to discuss asset counts. In Figure #11, you will notice at the start of the video the Photo Library Recents indicates there are 92 Photos and 12 videos. We can verify this by reviewing the syncstatus.plist, being stored at \private\var\mobile\Media\PhotoData\CPL\.
Does this asset count include the hidden assets?
In Figure #11 the Hidden assets utility is made visible and we can then check to see if any assets are hidden. After gaining access to the Hidden assets, we can see that there are 3 photos and 1 video currently being hidden. Let’s observe what happens to the counts after they are no longer hidden.
Our asset count is now 95 Photos and 13 Videos and verified via the syncstatus.plist. Then the assets are hidden again.
I continue to follow the chain of events, by analyzing the Photos.sqlite to locate the assets that are hidden. As mentioned previously, the ZASSET table ZHIDDEN column will contain the values you will want to analyze. Notice the original file name does not match the file name. This is the result of the assets being synced from iCloud Photos after a device reset. But you can notice on the device the original file name is written on a piece of paper that matches the ZADDITIONALASSETATTRIBUTES ZORIGINALFILENAME column data. Notice, the ZCLOUDMASTER table ZORIGINALFILENAME column data matches the previously mentioned original filename.
Where are Hidden Assets being stored?
Hidden asset(s) will be stored in the same file path regardless of the asset being Hidden or not. Example: If an non-hidden asset is being stored at \var\mobile\Media\DCIM\100APPLE, it will still be stored at this location after it is marked as Hidden. Figure #12 is a video illustrating Hidden assets and the file paths they are being stored.
Comparing the device assets to the iCloud Photos assets
In Figure #13, I will demonstrate a comparison to what is being stored on the device and being stored in the associated Apple ID iCloud Photos storage. We will also see evidence that these Hidden assets are not being stored in an album.
Photos.sqlite Queries
Here is a link to the full iOS 16 Photos.sqlite query. In the past, I have been hesitant to post smaller, artifact targeted, Photos.sqlite queries, because I feel that an analyst should review all available information when conducting an analysis. In this case, I have included links to two smaller queries that will provide result for the assets that have been marked as Hidden and different query for those assets that have been marked as Recently Deleted. I am doing this because there might be a instance where someone might not have access to the locked Hidden and Recently Deleted assets.
Future Work
This will have to be revalidated when iOS 16 is released to the public.
**Update 10/3/2022**
I have verified this material is applicable through iOS 16.0.2 (20A380)
Conclusion
Based on the version tested, iOS 16.0 (20A5303i) beta, I don’t believe the enhanced Hidden asset feature, the locking of hidden assets with a Passcode, Face ID, or Touch ID, will cause critical forensic challenges. It appears to be a simple feature enhancement that can be used by a device owner to hide assets from unauthorized users, not mobile forensicators.
This feature could cause difficulties during a manual examination when the passcode is unknown. If you can acquire an iTunes backup or the equivalent, you can analyze the Photos.sqlite database to determine how many assets you are not able to view during the manual exam.

This is very useful information about IOS 16
LikeLike
Hello, I am just wondering which software you are using to virtualize the test device?
LikeLike
I use Artifact Examiner (ArtEx) by Ian Whiffin of https://www.doubleblak.com/ to review the data. I use 3uTools and ApowerMirror for screen mirroring.
LikeLike